Master HMPL Development Offline With Our Free Advanced HMPL Render Studio
Master HMPL Development Offline With Our Free Advanced HMPL Render Studio Write, format,...

Master HMPL Development Offline With Our Free Advanced HMPL Render Studio Write, format,...
Master HMPL Development Offline With Our Free Advanced HMPL Render Studio Write, format, and preview your HMPL code offline with our free HMPL render studio. Features an AI generator, built-in mock API tester, and secure shareable links. 🟥 The Problem With Modern Server-Driven Testing If you build web applications today, you know the headache of … Read more

How to work Offline ShadCN UI Generator Master modern frontend architecture with our...
How to work Offline ShadCN UI Generator Master modern frontend architecture with our offline Tailwind component builder. Learn client-side DOM parsing while generating React and Vue UI components safely. 🟥 Why Front-End Engineering Needs a Client-Side Offline Tailwind Component Builder Modern frontend development operates at an incredibly fast pace. Engineers constantly prototype, design, and refactor … Read more

The Ultimate Guide to Secure Offline Web Development Utilities in 2026 Discover why...
The Ultimate Guide to Secure Offline Web Development Utilities in 2026 Discover why secure offline web development utilities are essential for modern coding. Protect your privacy and speed up workflows without cloud servers today. 🟥 The Death of Cloud-Based Code Formatting Every single day, senior programmers make a critical mistake. They copy sensitive code snippets. … Read more

Securing API Keys: How Client-Side Data Processing Protects Users Learn how client-side data...
Securing API Keys: How Client-Side Data Processing Protects Users Learn how client-side data processing protects user privacy, secures API keys, and prevents server-side breaches in modern offline web development. The Critical Need for Client-Side Data Processing When Handling API Keys Developers handle sensitive information every single day. From cloud provider API keys and database connection … Read more

Free Offline UUID GUID Generator Validator Tool Generate and validate primary keys securely...
Free Offline UUID GUID Generator Validator Tool Generate and validate primary keys securely with our free offline UUID GUID Generator Validator Tool. 100% client-side processing for ultimate data privacy. 🟥 Why Every Developer Needs a Free Offline UUID GUID Generator Validator Every time you create a new database record, issue a secure session token, or … Read more

Universal URL Encoder Decoder: The Ultimate Guide to Safe Links Discover how a...
Universal URL Encoder Decoder: The Ultimate Guide to Safe Links Discover how a universal url encoder decoder ensures your web links are safe, secure, and properly formatted. Learn the theory of percent encoding today! 🟥 The Complete Guide to Using a Universal URL Encoder Decoder Every single time you browse the internet, share a social … Read more
Free Offline Regex Tester: Debug Patterns Securely Debug regular expressions instantly with our...
Free Offline Regex Tester: Debug Patterns Securely Debug regular expressions instantly with our free offline regex tester. Master client-side pattern matching and secure your text data with zero latency today. 🟥 The Theoretical Framework of Pattern Matching In the highly analytical disciplines of software engineering, data science, and server administration, the ability to rapidly parse, … Read more
Free Offline Cron Job Generator: Master Server Automation Master time-based server automation with...
Free Offline Cron Job Generator: Master Server Automation Master time-based server automation with our free offline cron job generator. Discover the theoretical syntax of scheduling with zero server latency today. 🟥 The Theoretical Architecture of Time-Based Server Scheduling In the complex ecosystem of server administration, automated backend processes, and continuous integration pipelines, operational precision is … Read more
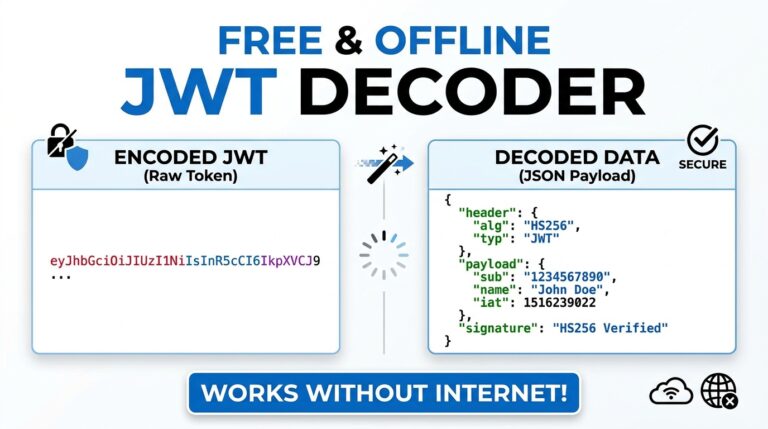
Free Offline JWT Decoder: Secure Your Token Analysis Debug API authentication instantly with...
Free Offline JWT Decoder: Secure Your Token Analysis Debug API authentication instantly with our free offline JWT decoder. Master client-side token parsing and secure your payload data with zero server latency. 🟥 The Theoretical Framework of Stateless Authentication In the highly secure architecture of modern web applications, stateless authentication has become the definitive standard for … Read more

Free Offline JSON Formatter Validator: Parse Securely Clean, validate, and convert complex data...
Free Offline JSON Formatter Validator: Parse Securely Clean, validate, and convert complex data structures instantly with a free offline JSON formatter validator. Ensure military-grade privacy and local execution. 🟥 The Theoretical Architecture of Data Serialization In modern software engineering, data serialization is the critical backbone of web communication. Representational State Transfer (REST) APIs, microservices, and … Read more